Most security professionals are familiar with at least a few of the high profile disclosures of spyware attacks such as the 2018 incident involving the nearly year-long surveillance of Jeff Bezos’s iPhone using Pegasus spyware. The attack was eventually attributed to Prince Mohammed bin Salman and carried out using a WhatsApp message.
Earlier this month, our team confirmed the presence of Pegasus on the phone of an Indian journalist who was reporting on corporate fraud and government corruption.
But it’s not only executives, journalists, or political dissidents being targeted anymore. It’s anyone whose phone might contain valuable information for adversaries, whose interests are becoming ever-more commercial.
According to the Carnegie Endowment for International Peace Report, “In addition to top-level commercial spyware vendors like NSO Group and Cytrox (now Intellexa), there is a burgeoning secondary tier of suppliers composed of boutique spyware firms, hacker-by-night operations, exploit brokers, and similar groups. As large commercial firms face greater scrutiny from democratic governments about their practices, there is a corresponding increase in open-source and commercially available malware.”
Even security companies aren’t immune to spyware attacks. In 2023, Operation Triangulation targeted iOS devices including those of Kaspersky employees by exploiting five vulnerabilities, four of which were previously unknown zero-days.
Additionally, as Nick Biasini from Cisco Talos Intelligence Group examined on a recent episodes of the Security Conversations podcast:
"The mercenary landscape is huge! For a state, a couple million dollars is nothing, but that gives them the capability to do some very sophisticated things and in the case of mercenary spyware or commercial spyware, compromise basically anyone who has a phone."
In short, now mercenary spyware is everyone’s problem - including enterprise security leaders.
The Business of Mobile Spyware
The mercenary spyware industry (yes, it’s accurate to now call it that) is valued at an estimated US$12 billion per year, according to the Center for International Governance Innovation. At least 75 countries - nearly 40 percent of all nations globally, have acquired commercial spyware within the last decade. While their primary customer continues to be governments, other customers have shown they are willing to use commercial social networks and mobile networks to launch large scale invasions of user’s private accounts and infiltrate the mobile phones of private sector employees.
The list of recent, and increasingly brazen mercenary spyware attacks is long, and growing all the time. Here are just a few:
Earlier this year, links to Predator were sprayed across X (formerly Twitter) in a dragnet that could have ensnared unintended victims in order to reach a handful of intended targets.
A Meta employee - from the company’s security team no less - had her phone hacked using Predator from Intellexa. According to The Predator Files report from Amnesty International, “highly invasive mobile spyware like Predator” can be delivered to devices using either 1-click attacks or 0-click attacks.
A spyware campaign which included zero-day exploits targeting Google’s Android operating system was discovered by Amnesty International's Security Lab. The exploit had the potential to affect billions of Android, Chrome and Linux users worldwide.
Microsoft researchers working with Citizen Lab published a report on a spyware exploit from an under the radar vendor, QuaDream, that Meta confirmed was also active on their platform.
Following the publication of the QuaDream research, Amy Hogan-Burney, associate general counsel for cybersecurity policy at Microsoft, highlighted the broader risks of mercenary spyware in a blog:
“Their actions do not only impact the individual they target, but leave whole networks and products exposed and vulnerable to further attacks.” And: “This poses real risk to human rights online, but also to the security and stability of the broader online environment.”
In other words, spyware is a real risk to the networks, products, and online presence of corporate enterprise.
Easy targets, few consequences: Why business is vulnerable to mercenary spyware
Even as enterprises harden their networks and devices to protect against intrusion, mobile phones - which often have access to valuable data and IP on a corporate network - continue to get short shrift and are a growing risk for advanced mobile threats. Security leaders need a full picture of the risk mercenary spyware poses to their organization in order to protect it.
Consider:
Today’s workforce is mobile-first. Yet protecting employee devices is often a lower priority than traditional enterprise security programs. And, mobile security solutions remain stuck in the past, relying heavily on management profiles that reduce device functionality and generate privacy concerns while offering little in the way of meaningful security.
This has not gone unnoticed by hackers, who know that spyware can penetrate the mobile phones of corporate employees (or their unwitting family members) to access highly confidential corporate data. The consequences of mobile breaches and data exfiltration include:
Corporate espionage, including intellectual property and trade secret theft
Blackmail and threats to physical safety, made easy by malware-as-a-service products available across the internet
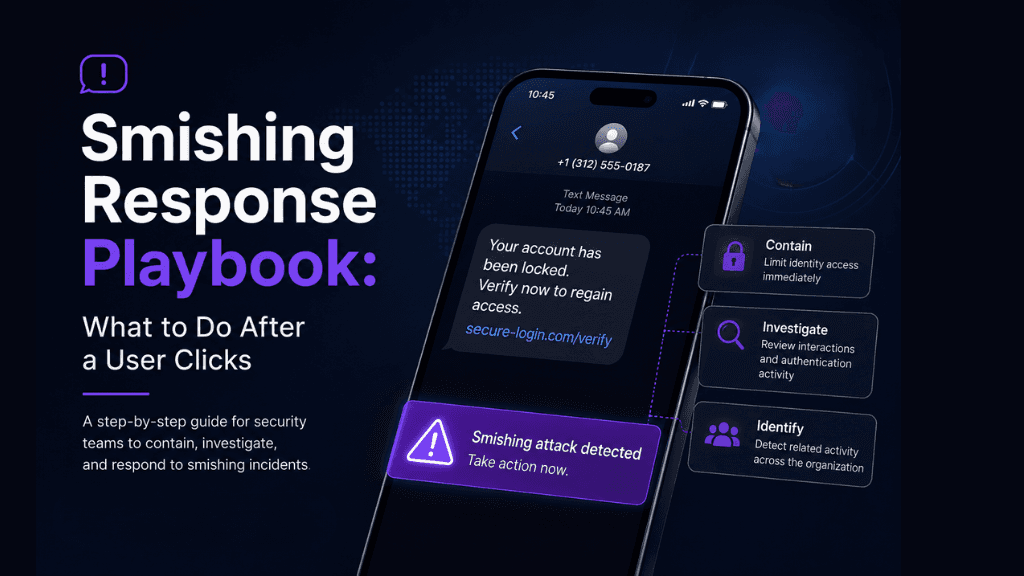
Credential theft to bypass enterprise security and MFA, which can perpetuate and exacerbate smishing and phishing attacks
Companies can be a trojan horse to access government employees or data. Tens of thousands of businesses are contractors with the U.S. government, including military contractors. They are a vulnerable link in the cyber supply chain. As CISA states, “The complexity and, to a degree, the proprietary nature and obscurity of ICT supply chains have made them increasingly at risk. This includes risk of exposure of sensitive or classified data that may imperil an organization’s mission.” Enterprises that count the government as a vital customer - and have access to sensitive information that mercenary spyware for hire attackers would love to access - need to understand that reaching it could be just a zero click exploit away.
Mercenary spyware actors know how to use the side door. CISOs sometimes forget that employees have a life outside of work - one that is much less secure than their work life. Social media platforms, risky apps, even family and friends are all potential gateways to reach a corporate employee when their guard is down - and gain access to their mobile device. Which, in this BYOD world, is both a personal and enterprise-connected tool. Mercenary spyware users are particularly skilled at this, having cut their teeth by targeting individuals through social media and the personal associates of targets to launch spyware attacks.
A new way to combat the mercenary spyware menace
Alarm bells have been going off for some time about the rise of mercenary spyware and the real harm it can do. Governments have tried to catch up - President Biden even signed an executive order prohibiting the U.S. government from using commercial spyware. Amnesty International, Citizen Lab, and other groups are constantly pushing to outlaw purveyors of spyware. And the NSO group is being sued by Meta and Jamal Kashoggi’s widow. Yet in their place, a plethora of spyware shops have sprung up. Many vendors are able to hide behind “legitimate” companies and often evade consequences - even when they’re caught. For security researchers, it’s like playing whack-a-mole to uncover, track and publish findings on all of these players. And corporate security teams can’t necessarily rely on researchers or the government to address the problem quickly or comprehensively. Most security teams are well aware of the risks; 55% of CISOs say phones are the most vulnerable node in the stack.
A new approach to protect against mobile mercenary spyware is needed. That’s why we exist. iVerify is the world’s first mobile threat hunting company providing elite cyber defense for mobile devices. We are the first solution focused on rooting out sophisticated mobile malware by scaling the process of mobile forensics. iVerify Enterprise monitors iOS and Android security telemetry without requiring, but enhancing, a management profile on the device when used together.
At the recent Objective by the Sea v6.0 conference, iVerify’s VP of Research, Matthias Frielingsdorf presented a talk entitled “Poisoned Apples - How Do We Find Them?” in which he provided updates on iOS malware research including Operation Triangulation, Pegasus 2023, and Quadream Reign.
“Even though it gets harder and harder to exploit iOS, we keep getting more vulnerabilities.” - Matthias Frielingsdorf, VP of Research, iVerify (“Poisoned Apples - How Do We Find Them?” presented at Objective by the Sea v6.0)
He also shared the forensic methods and types of IOCs used to detect them – and how companies can create their own forensic artifacts for analysis using backups, sysdiagnose, and crash reports.
We outlined these methods in a previous blog post. You can also watch the recording of Matthias’ talk at: https://youtu.be/m_RTWaBkEwk?si=t53reK5Vasv-cPYv.
Soon, will we announce a new solution designed specifically to address the growing risk mercenary spyware poses to businesses. Stay tuned!
Matthias Frielingsdorf, VP of Research
Jelmer de Hen, Head of Android R&D
Subscribe to our blog to receive the latest research and industry trends delivered straight to your inbox. Our blog content covers sophisticated mobile threats, unpatched vulnerabilities, smishing, and the latest industry news to keep you informed and secure.