Featured on
Exploit scarcity is dead
~90%
MOBILE THREAT DEFENSE IS DEAD
Legacy MTD Solutions
Signatures.
Network-dependent.
Blind to the kernel.
Tricks, not telemetry
Conflicts with VPNs
Stagnant against AI-Driven exploits
iVerify Mobile EDR
Operating system telemetry.
Behavioral baselining.
Threat hunting at AI speed.
Process, file system, crash logs, and memory monitoring
Stands alone — no network VPN required
Near-zero false positives on critical alerts
You can't stop the threats you can't see
Employees use their phones to access corporate applications where they receive MFA codes, store session tokens, and handle sensitive communications, but unlike laptops and servers, mobile has operated with little to no visibility until now.
SOC Coverage Gap
Your SOC sees every endpoint, except the one in every pocket.
Active Compromise
MDM reports compliance. It can't report compromise.
Exposed BYOD
Personal devices reach corporate systems without security visibility.
Malware and Spyware
Detect Pegasus, Coruna, and DarkSword before they reach your data.
Enterprise Account Takeover
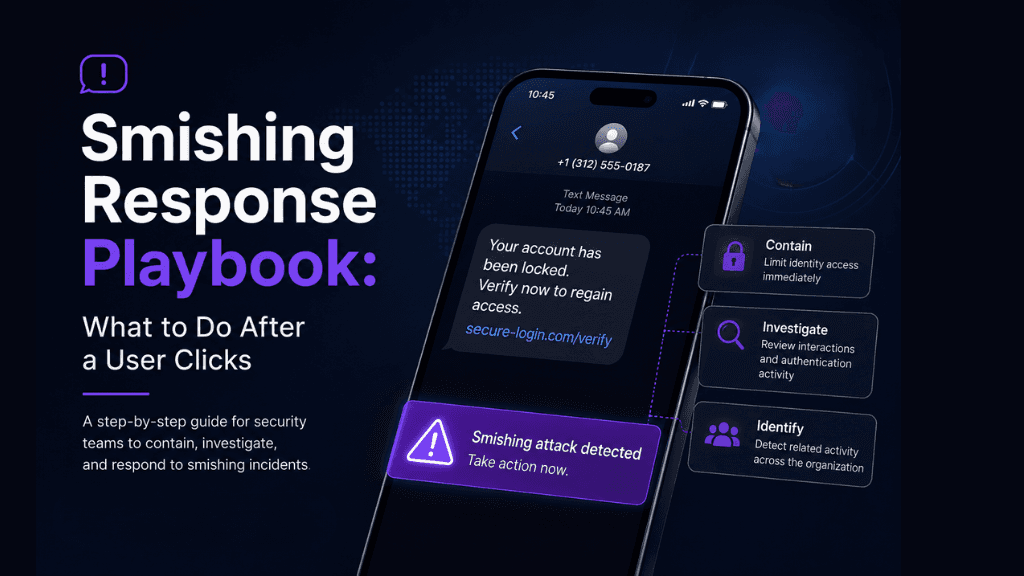
Stop smishing, vishing, and SIM swap at the source.
High-Risk Travel
The threat model changes the moment your employees board a plane.
AI-Accelerated Exploitation
AI closed the gap between vulnerability disclosure and active exploit.
Mobile App Vetting
Every approved app is a data leak vector, including shadow AI.
What makes iVerify different
LEARN FROM OUR TEAM